David Ronfeldt at RAND just sent me his new (co-authored) piece on “The Prospects for Cyberacrocy” which I found particularly interesting given the contrast to his original paper of the same name in 1992. David’s timing is impeccable since I am co-teaching a course on Digital Democracy with my colleague Joshua Goldstein. The course is being offered this Spring semester as part of the interdisciplinary Media and Commincation Studies Program at Tufts University.
Since David’s paper is 70 pages long, what follows is a concise 5-page summary with references to additional contemporary works (e.g., by Clay Shirky, Yochai Benkler, Antony Loewenstein, etc.), and current examples written specifically for our Digital Democracy students.
In 1992, David Ronfeldt wrote that a “precise definition of cyberocracy was not possible at present.” In a general sense, then, he identified two ways in which cyberocracy may manifest itself:
- Narrowly, as a form of organization that supplants traditional forms of bureaucracy and technocracy;
- Broadly, as a form of government that may redefine relations between state and society, and between the public sector and the private sector.
Ronfeldt cautions that optimism about the information revolution should be tempered by an anticipation of it’s potential dark side. He contrasts term cyberocracy with aristocracy and theocracy—under which the high-born and high priests ruled respectively. The author argues that cyberocracy, a product of the information revolution, may slowly but radically affect who rules, how and why. That is, “information and its control will become a dominant source of power, as a natural next step in political evolution.”
Clay Shirky would certainly agree. “When we change the way we communicate, we change society. The tools that a society uses to create and maintain itself are as central to human life as a hive is to bee life.” However, “the mere tools aren’t enough. The tools are simply a way of channeling existing motivation.”
Citing earlier research, David suggests that consequences of new technology can be usefully thought of as first-order and second-order effects. The first-order effect can be framed as gains in efficiency. “The history of previous technologies demonstrates that early in the life of a new technology, people are likely to emphasize the efficiency effects and underestimate or overlook potential social system effects.”
The second-order effects bring about behavioral and organizational change which affect how people think and work together. New systems of thought are thus generated by second-order effects. “The major impact will probably be felt in terms of the organization and behavior of the modern bureaucratic state.” Take the printing press, for example, “it created conditions that favored, first, new combinations of old ideas and, then, the creation of entirely new systems of thought.”
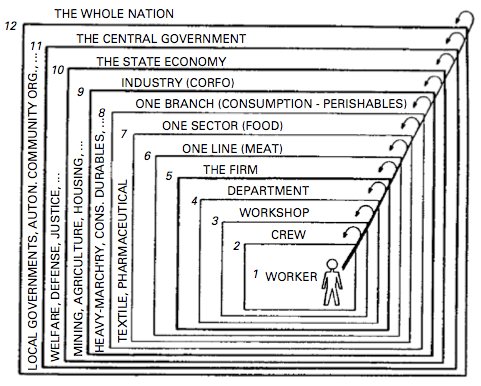
In “Seeing Like a State,” James Scott explains why certain state-centered schemes to improve the human condition have failed. Scott writes that “no administrative system is capable of representing [or monitoring] every existing social community except through a heroic and greatly schematized process of abstraction and simplification.” David Ronfeldt provides additional insight: “the hierarchical structuring of bureaucracies into offices, departments, and lines of authority may confound the flow of information that may be needed to deal with complex issues in today’s increasingly interconnected world.”
Would a cyberocracy provide a more effective political template to improve the human condition? Ronfeldt might be tempted to answer in the affirmative. Clay Shirky [2008] and Yochai Benkler [2006] would not hesitate to reply with a resounding yes.
Ronfeldt writes that “bureaucracy depends on going through channels and keeping information in bounds; in contrast, cyberocracy may place a premium on gaining information from any source, public or private. Technocracy emphasizes ‘hard’ quantitative and econometric skills, like programming and budgeting methodologies; in contrast, a cyberocracy may bring a new emphasis on ‘soft’ symbolic, cultural, and psychological dimensions of policymaking and public opinion.”
As Clay Shirky notes, “if you want to organize the work of even dozens of individuals, you have to manage them. As organizations grow into the hundreds or thousands, you also have to manage the managers, and eventually to manage the managers’ managers. Simply to exist at that size, an organization has to take on the costs of all that management.” This template is hardly likely to improve today’s interconnected challenges.
In “Wealth of Networks“, Benkler writes that the “actual practice of freedom that we see emerging from the networked environment allows people to reach across national or social boundaries, across space and political division. It allows people to solve problems together in new associations that are outside the boundaries of formal, legal-political association.”
Writing in the early 1990s, pioneer computer technologist Alan Kay anticipates the rise of blogs which are in effect new types of associations that stand outside of traditional boundaries (cited in Ronfeldt): “The retrieval systems of the future are not going to retrieve facts but points of view. The weakness of databases is that they let you retrieve facts, while the strength of our culture over the past several hundred years has been our ability to take on multiple points of view.”
However, authoritarian regimes (and some democratic ones according to Noam Chomsky), typically crack down on the ability of individuals to express multiple points of view. Writing in 1992, Ronfeldt states that “some of today’s trendier points—e.g., the information revolution empowers individuals, favors open societies, and portends a worldwide triumph for democracy—may not hold up as times change.”
Ronfeldt suggests that the information revolution will foster more open and closed systems; more decentralization and centralization; more inclusionary and exclusionary communities; more privacy and surveillance; more freedom and authority; more democracy and new forms of totalitarianism.
Ronfeldt provides a superb critque of those who maintain that decentralization and networks explain and ensure the success in the new business environment. However, “complex organizations depend on some kind of hierarchy. Hierarchy does not end because work teams include people from different levels and branches. The structure may be more open, the process more fluid, and the conventions redefined; but a hierarchy still exists.”
The consequence of the information revolution may thus mean “greater decentralization for highly centralized organizations, and greater centralization for decentralized ones.” On the other hand, if new technology does foster decentralization, “it may also provide greater ‘topsight‘—a central understanding of the big picture that enhances the management of complexity.” The pursuit of topsight is thus the pursuit to understand the big picture, “the most precious intellectual commodity known to man.”
A question of interest to me given my dissertation research is whether repressive regimes will/do have the ability to retain the upper hand in using new technology to maintain information supremacy within their borders. Ronfeldt touched on this question in 1992. “As cyberocracy develops, will governments become flatter, less hierarchical, more decentralized, with different kinds of middle-level officials and offices? Some may, but many may not. Governments [particularly repressive regimes] may not have the organizational flexibility and options that corporations have.”
Along these lines, former US Secretary of State George Shultz argued in 1985 that information and communication flows can be used as a powerful instrument for compelling closed societies to open up. At the time, Schulz wrote that communist states fear the information revolution perhaps more than they fear Western military strength. “The revolution in global communications thus forces all nations to reconsider traditional ways of thinking about national sovereignty.”
Ronfeldt summarizes Shulz’s take on the “dictator’s dilemma“: if the Soviet regime risked adopting new technologies, it’s leaders would have to liberalize the Soviet economic and political systems, which is arguably what happened. Ronfeldt thus writes that as “long as the aim in the West is the demise of communist and other traditional hard-line authoritarian systems, policymakers in the United States and Europe are well advised to expect that the diffusion of the new technologies will speed the collapse of closed societies and favor the spread of open ones.”
This is (still) the current US policy towards Cuba, for example. In his recent book, “The Blogging Revolution,” Antony Loewenstein notes that,
“Cuba’s official Communist organ Gramma International reported in June 2008 that a meeting in Washington in May discussed using USAID to ‘promote the clandestine dispatch of electronic materials to the island via European and Latin American intermediaries’. The aim of the US$45 million was to distribute ‘propaganda pamphlets, cell phones and modern communications equipment’ and ‘train Cubans resident in third countries.’
George W Bush has publicly stated that he wanted to use the Internet to destabilize the Cuban Government. In May 2001, Bush gave a speech in which he advocated the Internet as just one tool to weaken Castro, and the 2006 Commission for Assistance to a Free Cuba Report state that US$24 million was being spent on ‘efforts to break the Cuban government’s information blockade and expand access to independent information, including through the Internet’.”
As Ronfeldt noted in 1992, however, “the fact that the new technology can help sweep aside old types of closed regimes does not necessarily mean that it will also make democratic societies more democratic, or totalitarian ones impossible.” Indeed, “a longer view of history provides little assurance that the new technology favors democracy.”
As Ronfeldt wrote, “the printing press and later technologies, like the telephone and radio, did not prevent new and ever worse forms of autocracy from arising.” While these technologies undermined the power base of old monarchies, these same technologies were subsequently “turned into tools of propaganda, surveillance, and subjugation that enabled dictators to seize power and develop totalitarian regimes.”
Ronfeldt maintains that technology is not neutral or apolitical but it does “widen the range of possibilities within a particular context.” But as Clay Shirky notes, “arguments about whether new forms of sharing or collaboration are, on balance, good or bad reveal more about the speaker than the subject.”
In any case, the effect of technology depends on context. Ronfeldt cites Daniel Bell (1979) to explain that “the new revolution in communications makes possible both an intense degree of centralization of power, if the society decides to use it in that way, and large decentralization because of the multiplicity, diversity, and cheapness of the modes of communication.”
Ronfeldt adds that “the existence of democracy does not assure that the new technology will strengthen democratic tendencies and be used as a force for good rather than evil. The new technology may be a double-edged sword even in a democracy.” To this end, “far from favoring democracy or totalitarianism, cyberocracy may facilitate more advanced forms of both. It seems as likely to foster further divergence as convergence, and divergence has been as much the historical rule as convergence.”
Furthermore, Ronfeldt argues that while “in the past the divergence principle was most evident between countries,” a future possibility “is that the principle may increasingly apply within countries. The information revolution may enable hybrid systems to take form that do not fit standard distinctions between democracy and totalitarianism. In these systems, part of the populace may be empowered to act more democratically than ever, but other parts may be subjected to new techniques of surveillance and control.”
A question that naturally follows is whether cyberocracy will spell the obsolescence and transformation of standard Marxist theses. While Marxism claimed that “capital accummulation” faciliated political exploitation, would Marx not focus instead on “information” if he were to reappear today? Ronfeldt suggests that information may very well come to “succeed capital as a central theoretical concept for political and social philosophy” in the post-industrial age.
According to Marxism, the capitalist accumulation of “surplus labor” and labor’s exploitation by “monopoly capital” account for a society’s structure and its ills and inclinations. That structure is composed of socioeconomic “classes” that are defined by the “relation to the means of production of capital.”
But the post-industrial age may instead raise a new concern about “surplus information” or “monopoly information” that is concentrated, guarded, and exploited for privileged economic and political purposes. Moreover, a society may become structured into new kinds of classes depending on one’s relation to the means of production of information.
The above summarizes Ronfeldt’s Cyberocracy paper from 1992. The following is a summary of his 2008 postscript co-authored with Danielle Varda.
Ronfeldt and Varda conclude that “influence in the information age is indeed proving to revolve around symbolic politics and media savvy — the ‘soft power’ aspects of influence.” Based on the evidence of the past 18 years, the authors also conclude that “the information revolution continues to enable both democratic and totalitarian tendencies. […] The information age is indeed leading to new hybrid amalgams of democratic and authoritarian tendencies, often in the same country.” The authors also conclude that “governments are still straining to adapt. Bureaucracy remains the rule, cyberocracy a speculation.”
In terms of next steps for further research, Ronfeldt and Varda outline four speculations about future trends:
- The advanced societies are developing new sensory apparatuses that people have barely begun to understand and use;
- A network-based social sector is emerging, distinct from the traditional public and private sectors. Consisting largely of NGOs and NPOs, its rise is leading to a re-balancing of state, market, and civil-society forces;
- New modes of multiorganizational collaboration are taking shape, and progress toward networked governance is occurring;
- This may lead to the emergence of the nexus-state as a successor to the nation-state.
The authors argue that people and organizations in “advanced societies” are “building vast new sensory apparatuses for watching what is happening in their own societies and around the world. Of all the uses to which the new technologies are being put, this may become one of the most important for the future of the state and its relationship to society.” The rise of citizen journalism is certainly a significant consequence of the information revolution.
Ronfeld and Varda point out that “many of the new apparatuses reflect the perception of perils. Crime and terrorism are impelling new installations for watching cityscapes, monitoring communications, and mapping potential hotspots. But sensor networks are also being deployed for early warning and rapid response regarding many other concerns — disease outbreaks, forest protection, [etc.].”
In addition, the authors argue that “environmental, human-rights, and other social activists continue to develop new media to keep watch and speed mobilization in case of a challenge or abuse somewhere […].” Examples include DigiActive, Digital Democracy 2.0, Witness, Ushahidi, and Global Voices. Indeed, Ronfeldt and Varda suggest that citizens’ concerns about top-down surveillance may be countered by bottom-up “sousveillance” (or inverse surveillance), particularly if individuals wear personal devices for detecting and recording what is occurring in their vicinity.”
Ronfeldt and Vera maintain that new sensory apparatuses will accelerate the “rise of civil-society actors, by providing networked [actors] with new tools not only for checking on the behavior of government and corporate actors, but also for participating in collaborative governance schemes with them. New mechanisms for attracting and combining diverse viewpoints under the rubric of ‘collective intelligence’ could help foster this. So could the continued advance of principles favoring freedom of information, the right to communicate, and open access.”
While networks are as old as hierarchies and markets, the authors argue that they are “only now coming into their own as a major societal organizing principle. To function well on a large scale, multiorganizational networks require complex information and communications systems—even more than do hierarchies and markets—and those systems are finally afforded by the Internet and other new digital technologies.”
Clay Shirky would certainly agree with this conclusion. He writes that “we now have communications tools that are flexible enough to match our social capabilities, and we are witnessing the rise of new ways of coordination action that take advantage of that change.”
Ronfeld and Varda argue that civil society stands to gain the most from the rise of networks since “policy problems have become so complex and intractable, crossing so many jurisdictions and involving so many actors, that governments should evolve beyond the traditional bureaucratic model of the state.”
To this end, “a less hierarchical, more decentralized, pro-partnership model is needed, one that relies more on outsourced market measures and collaborative network designs. Metaphorically, this means a state that is less about (vertical) stovepipes and silos, and more about (horizontal) webs, bridges, and pools—a state where issues are deliberated less in channels and more on platforms.”
Ronfeldt and Varda forsee that “the evolution of network forms of organization and related doctrines, strategies, and technologies will attract government policymakers, business leaders, and civil-society actors to create myriad new mechanisms for communication, coordination, and collaboration spanning all levels of governance. Aging contentions that ‘the government’ or ‘the market’ is the solution to particular public-policy issues will give way to inspired new ideas that, in some areas, ‘the network” [or, in my opinion, ‘the ecosystem’] is the solution.'”
Returning to the question of hierarchies versus networks, Ronfeldt and Varda maintain that “states, not to mention societies as a whole, cannot endure without hierarchies. Familial tribes and clans were the first major form of organization to arise centuries ago; hierarchical institutions were second—and the state remains the home realm of this form. Information-age government may well undergo ‘reinventing’ and be made flatter, more networked, decentralized, etc.—but it will still have hierarchy at its core.”
In conclusion, Ronfeldt and Varda argue that the rise of the “Nexus-State” does not imply the weakening of the “traditional state.” To be sure, “the rise of the market system had those effects on the state, beginning a few centuries ago. As the state relinquished the control of commercial activities to private companies, both the nation and the state became stronger. Likewise, as the social sector expands and activities are transferred to it, the state should again emerge with a new kind of strength, even though it loses some scope in some areas.”
Only time will tell. I look forward to David’s update in 2020!
Patrick Philippe Meier