Before emergency telephone numbers existed, one would simply pick up the receiver and say “get me the police” when the operator answered. In fact, operators became the first point of contact for emergency dispatch. They would keep lists of specific numbers in their local towns (local fire department, local doctor, etc) to provide a very personalized emergency service and fast track response.

London was the first city to deploy an emergency number system. The number 999 was launched on June 30, 1937. When called, “a buzzer sounded and a red light flashed in the exchange to attract an operator’s attention” (1). The first number to be used in North America was the 911 system deployed in Winnipeg, Canada in 1959. The first US system, also using the 911 number, was launched in Alabama and Alaska in 1968. It wasn’t until the 1980s, however, that 911 was adopted as the standard number across most of the country.
Today, about 240 million 911 calls are made in the US each year, 30%-50% of which are placed using wireless services, and this number is increasing steadily.
When discussing the use of crowdsourcing to collect crisis information in humanitarian disasters, one of the overriding concerns is: “But what if the information is false? How can we trust that the information reported is true?” We forget that national emergency telephone systems have faced the same challenge for half-a-century. Indeed, 911 is a 50 year-old crowdsourcing system! So our colleagues in law enforcement may have learned a few things during this time, which could inform our work in the humanitarian field.
Incidentally, this may be a silly question but why in the world did governments set up emergency phone numbers if the information collected using this crowdsourced approach is not immediately verifiable? Have the police gone nuts? What were/are they thinking? Were police crowdsourcing reports before telephone lines sprung up across the country? Maybe one had to run, bike or drive to the police station. Or if you were lucky, perhaps you’d have a police officer strolling the streets at just the right time.
So why not keep that good old analog system then? Well, lets face it, do we really want to leg it to the station every time something’s strange in the neighborhood? No, we want to be able to call…

Can we assume that we’ll always be mobile during an emergency? Do we want to leave it up to chance that a fire truck might be patrolling the streets when the house next door house goes up in flames? Probably not.
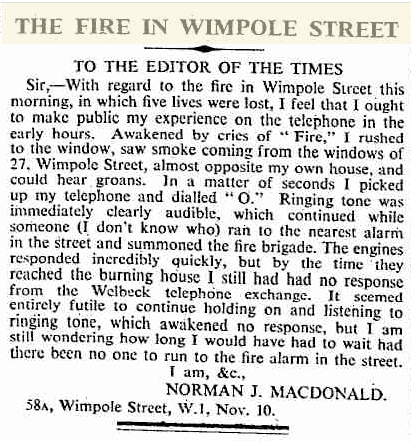
In fact, the world’s oldest emergency (crowdsourcing!) call service—the UK’s 999—was introduced over 70 years ago after a London fire on November 10, 1935 killed 5 women. A neighbor had tried to phone the fire brigade but was held up in a queue by the telephone exchange. Neighbor Norman was so outraged that he wrote a letter to the editor of The Times:
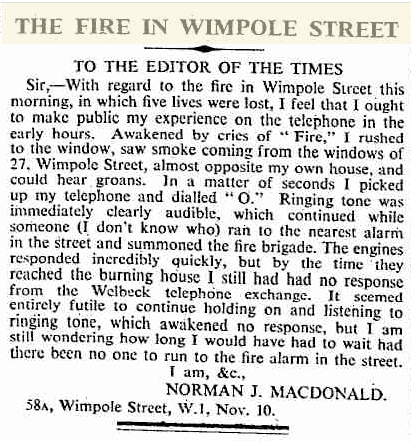
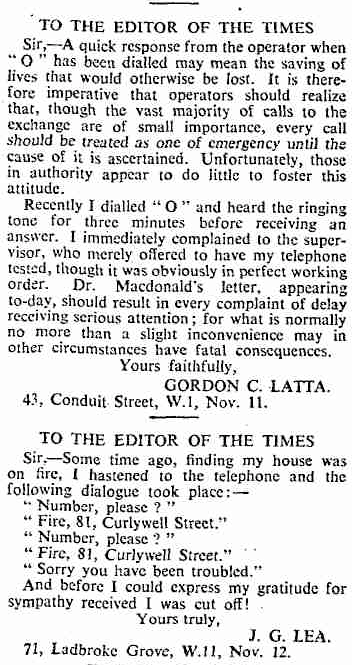
A public outcry resulted (which could have been crowdsourced and mapped on an Ushahidi platform as a complaints mechanism):

This prompted a government inquiry. And thus was born the largest crowdsourcing system of the day. Rather ironic that it was ultimately user generated content that created today’s national emergency phone services. Wouldn’t it be great to get a UN inquiry along those same lines that established a crowdsourcing system for humanitarian crises? Sounds crazy, I know, but hey, 999 probably sounded a little nuts back in 1937 as well. And yet, they decided to test the idea in London, then extended trials in Glasgow and within 10 years the entire country was covered. I don’t see why a similar iterative approach couldn’t work in disaster response.
But what challenges does an emergency phone system face? The misuse and abuse of 911 can be divided into 2 categories: unintentional and intentional calls (2). The former includes phantom calls, misdials and hang-up calls. Lets focus on the latter issue, which be divided into the following categories: Non-emergency Calls, Prank Calls, Exaggerated Calls and Lonely Complainant Calls.
- Non-emergency Calls: reports suggest that non-emergency calls account for a large percentage of 911 calls. For example, callers will phone in to report their car radio getting stolen, or ask for the results of a football game, the time of day, etc. 911 operators even get callers who ask them to transfer their calls to another number since calling 911 is free.
- Prank Calls: most agencies apparently do not keep figures on total number of prank calls but these generally come from children and teenagers. Diversionary calls represent a sub-category of prank calls. Callers will dial 911 to send the police to a location where not emergency has occurred, sometimes to divert attention away from criminal activity committed by the caller. “There are only a few ways to determine if a call is diversionary: if the caller admits it; if someone informs on the caller; or if the dispatcher or police compare the caller’s location with that of the alleged emergency, to determine if the caller could plausibly claim an emergency at the called in location” (4).
- Exaggerated Emergency Calls: callers will sometime intentionally exaggerate the seriousness of an emergency expecting that the police will respond faster. It is reportedly unclear how extensive this problem is.
- Lonely Complainant Calls: other callers will repeatedly report an emergency over a series of month or years but the police never find evidence of there being one. These calls are often made by the elderly and those with mental health problems.
As these news articles here & here show, false reports to 911 can claim lives. Does this mean that law enforcement is considering pulling the plug on the 911 system? Of course not. So how does law enforcement deal with all this? Lets stick to prank and diversionary calls since this comes closest to the most pressing concerns we face in the humanitarian context. (Note the other issues listed above are typically addressed by educating the public).
Law enforcement’s response to prank calls involves targeting violators and applying graduated sanctions, such as fines or jail time. In Ohio, a public service announcement made clear to users that “we know where you are” when you call 911. Prank calls reportedly dropped as a result (5). Police can also take action by targeting specific phones that are used for prank calls. In another example, a hotel in Vegas routed all 911 calls to hotel security for triage after a large number of false 911 reports were made to the fire department.
Could we do something similar within a humanitarian operation? There’s already precedent to prosecute hate-based SMS, as happened in Kenya. We could work with telcos in question to send out a mass SMS broadcast to all subscribers letting them know they can be prosecuted for deliberately reporting false information.
That’s not a silver bullet, of course, but it seems to help national emergency phone systems. We could also draw on natural language processing (NLP) technologies like Swift River to create veracity ratings for crowdsourced reports. Of course, when confronted with a major disaster, everyone may be calling 911 at the same time, thus overwhelming capacity to respond.
In terms of this operational response, one partial answer may be revitalizing Community Emergency Response Teams (CERTs). Another partial answer may be the idea of crowdfeeding, or crowdsourcing response as I blogged about here based on a recent presentation I gave at Red Cross Conference in DC. During that same conference, the Red Cross revealed the results of a study on the role of social media in emergencies, which showed that more than 70% of those surveyed expect a response within an hour after posting a request on an social media platform. Now, there are too few disaster response professionals to assign to every street to meet those expectations (not to mention the cost implications). So they can’t always be there, but the crowd, by definition, is always there.
In the case of national phone emergency systems, there are usually laws that require the police to respond (not that they always do). This may be difficult to work out in the context of humanitarian response. So let me share an anecdote from the Ushahidi-Haiti Project. One of our overriding concerns after launching the 4636 short code with colleagues was raising expectations among those texting that someone would respond to these SMS’s. Three points:
1) Colleagues and I spent hours on Haitian Diaspora radio and television answering questions from listeners and viewers about the purpose of 4636. We made it very clear that the service was simply an information service and that we couldn’t guarantee any kind of response. We also explained that some responders like the US Coast Guard and Marine Corps were prioritizing life and death situations and therefore were not responding to every text message. This helped callers understand the purpose and limits of the service.
2) As a result of these concerns regarding expectations, my colleague Jaroslav Valuch and I recommended that PakReport.org adjust their public messaging campaign by asking people to report their observations instead of their needs. One could also invite people to text in their complaints, thus crowdsourcing perceptions (real or otherwise) of frustration and discontent which could provide humanitarians with important situational awareness. But this too may raise expectations of response. So sticking with simple reports based on observations is sometimes more prudent.
3) As studies from Aceh (the 2004 tsunami) and Pakistan (the 2005 earthquake) showed, it is important to communicate with disaster affected communities, even if the message is that help is not yet on the way. See Imogen Hall’s research and the CDAC consortium, for example.
I’m using the 911 emergency system as an analogy and don’t pretend that the model can be automatically applied to the humanitarian context. But these phone-based emergency crowdsourcing systems have been around for half-a-century and it would be naive to discount any of the lessons learned and best practices that this wealth of experience has produced across such a large scale.
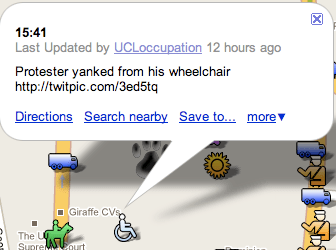
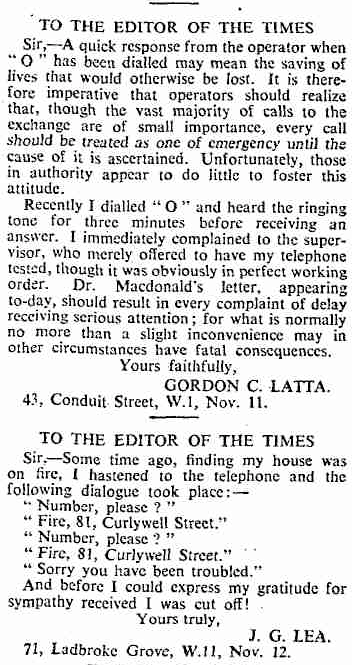
 The students also caught the following picture:
The students also caught the following picture: