The Chair of my dissertation committed, Professor Dan Drezner just published this piece in the Brown Journal of World Affairs that directly relates to my dissertation research. He presented an earlier version of this paper at a conference in 2005 which was instrumental in helping me frame and refine my dissertation question. I do disagree a bit with the paper’s approach, however.
Professor Drezner first reviews the usual evidence on whether the Internet empowers coercive regimes at the expense of resistance movements or vice versa. Not surprisingly, this perusal doesn’t point to a clear winner. Indeed, as is repeatedly stated in the academic discourse, “parsing out how ICT affects the tug-of-war between states and civil society activists is exceedingly difficult.”
Drezner therefore turns to a transaction costs metaphor for insight. He argues that “metaphorically, the problem is akin to the one economists faced when predicting how the communications revolution would affect the optimal size of the firm.” I’m not convinced this is an appropriate metaphor but lets proceed and summarize his reasoning on firm size in any case.
Economists argue that the size of a firm is a function of transaction costs. “If these costs of market exchange exceed those of more hierarchical governance structures—i.e., firms—then hierarchy would be the optimal choice. With the fall in communication costs, economists therefore predicted an associated decline in firm size. “There were lots of predictions about how the communications revolution would lead to an explosion in independent entrepreneurship.”
But Drezner argues that decreasing communication costs (a transaction cost) has not affected aggregate firm size: “Empirically, there has been minimal change.” Unfortunately, he doesn’t cite any literature to back this claim. Regardless, Drezner concludes that firm size has not significantly changed because “the information revolution has lowered the organizational costs of hierarchy as well” and even “increased the optimal size of the firm” in some sectors. “The implications of this [metaphor] for the internet’s effect on states and civil society should be apparent.”
The problem (even if the choice of metaphor were applicable) is that these implications provide minimal insight into the debate on liberation technologies: large organizations or institutions have the opportunity to scale thanks to the Internet; meaning that government monitoring becomes more efficient and sophisticated, making it “easier for the state to anticipate and regulate civic protests.” More specifically, “repressive regimes can monitor opposition websites, read Twitter feeds, and hack e-mails—and crack down on these services when necessary.” Yes, but this is already well known so I’m not sure what the transaction metaphor adds to the discourse.
That said, Drezner does recognize that the Internet could have a “pivotal effect” on state-society relations with respect to “authoritarian and semi-authoritarian states that wish to exploit the economic possibilities of the information society.” Unfortunately, he doesn’t really expand on this point beyond the repeating the “Dictator’s Dilemma” argument. But he does address the potential relevance of “information cascades” for the study of digital activism in non-permissive environments.
“An informational cascade takes place when individuals acting in an environment of uncertainty strongly condition their choices on what others have done previously. More formally, an information cascade is a situation in which every actor, based on the observations of others, makes the same choice independent of his/her private information signal. Less formally, an information cascade demonstrates the power of peer pressure—many individuals will choose actions based on what they observe others doing.”
So if others are not protesting, you are unlikely to stick your neck out and start a protest yourself, particularly against a repressive state. But Drezner argues that information cascades can be reversed as a result of a shock to the system such as an election or natural disaster. These events can “trigger spontaneous acts of protest or a reverse in the cascade,” especially since “a little bit of public information can reverse a long-standing informational cascade that contributed to citizen quiescence.” In sum, “even if people may have previously chosen one action, seemingly little information can induce the same people to choose the exact opposite action in response to a slight increase in information.”
This line of argument seems to cast aside what has been learned about civil disobedience. Drezner suggests that reverse information cascades can catalyze spontaneous protests. Perhaps, but are these “improvised” protests actually effective in achieving their stated aims? The empirical evidence from the literature on civil resistance suggests otherwise: extensive planning and strategizing is more likely to result in success then unplanned spontaneous protests. If I find out that it’s cooler in the frying pan than the fire, will I automatically jump into said pan? A little bit of additional information without prior planning on how to leverage that information into action can be dangerous and counterproductive.
For example:
“The spread of information technology increases the fragility of information cascades that sustain the appearance of authoritarian control. This effect creates windows of opportunity for civil society groups.”
Yes, but this means little if these groups are not adequately prepared to deliberately exploit weaknesses in authoritarian control and cash in on this window of opportunity.
“At moments when a critical mass of citizens recognizes their mutual dissatisfaction with their government, the ability of the state to repress can evaporate.”
Yes, but this rarely happens completely spontaneously. Undermining the pillars of power of a repressive state takes deliberate and calculated work with an appropriate mix of tactics and strategies to delegitimize the regime. There is a reason why civil resistance is often referred to as (nonviolent) guerrilla warfare. The latter is not random or haphazard. Guerilla campaigns are carefully thought through and successful actions are meticulously planned.
Drezner argues that, “Extremists, criminals, terrorists, and hyper-nationalists have embraced the information society just as eagerly as classical liberals.” Yes, this is already well known but the author doesn’t make the connection to training and planning on the part of extremists. As Thomas Homer-Dixon notes in his book The Upside of Down: “Extremists are often organized in coherent and well-coordinated groups that have clear goals, distinct identities, and strong internal bonds that have grown around a shared radical ideology. As a result, they can mobilize resources and power effectively.” Successful terrorists do not spontaneously terrorize! Furthermore, they create information cascades as much as they react to them.
In conclusion, Drezner criticizes the State Department’s Civil Society 2.0 Initiative. State presumes that technologies will primarily help the “good guys” and “assumes that the biggest impediment to the flowering of digital liberalism comes from the heavy hand of the state.” (He doesn’t say what the biggest impediment is, however). Drezner ends his piece with the following: “It is certainly possible that the initiative fails because of the coercive apparatus of a repressive government. It is equally likely, however, that the initiative succeeds—in empowering illiberal forces across the globe.” This is already well known. I’m not sure that one needs a transaction metaphor or to refer to the dictator’s dilemma, information cascades, spontaneous protests and extremist groups to reach this conclusion.

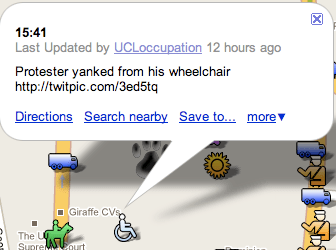
 The students also caught the following picture:
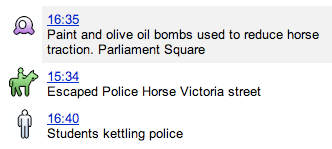
The students also caught the following picture: